Know what is online
Fast host discovery, flexible target input, MAC vendor lookup, hostname resolution, service detection, and optional passive evidence from mDNS, SSDP, and DHCP.
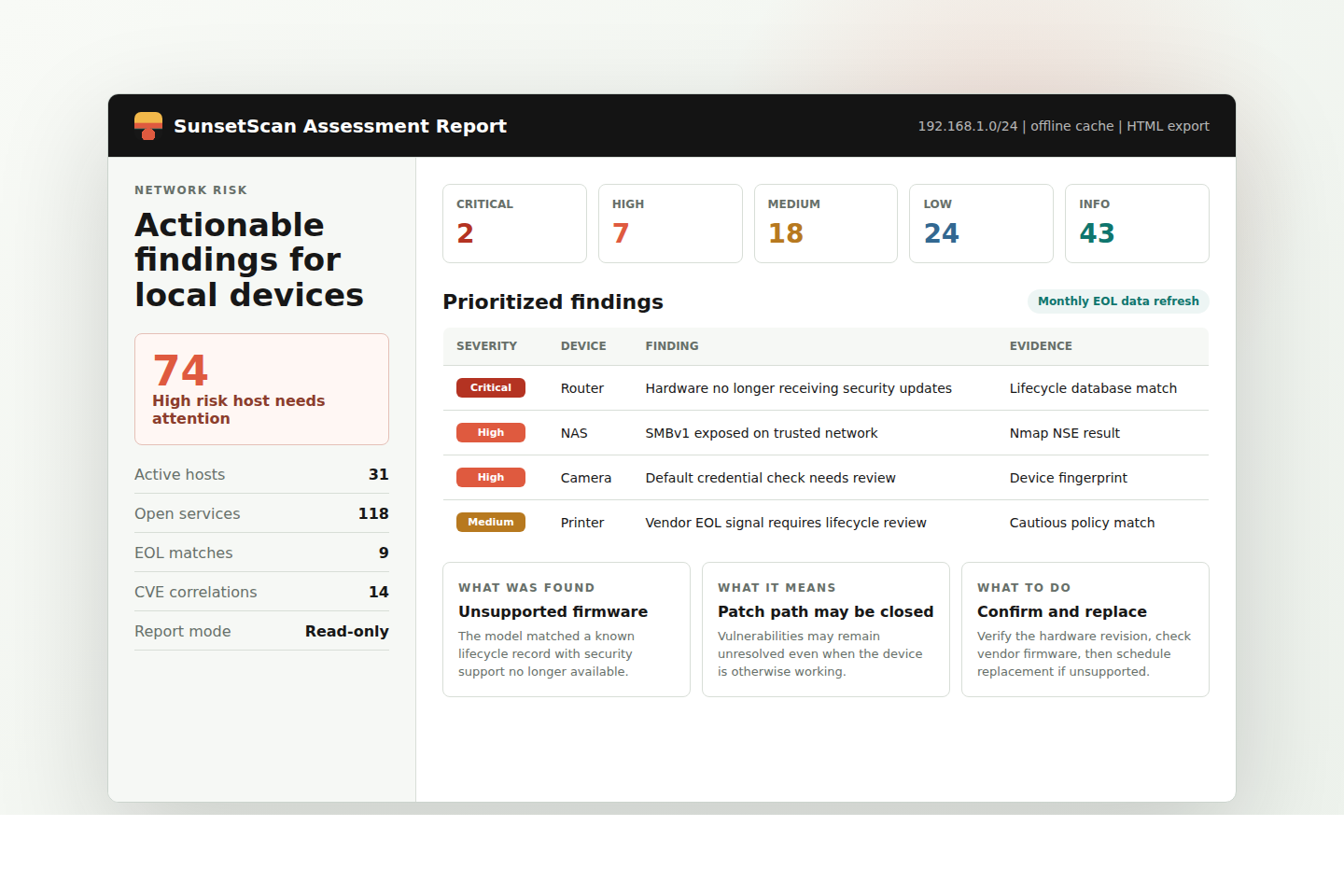
Open-source local network security auditing
Find unsupported devices, exposed services, weak configurations, and fixable security risks across your local network.
SunsetScan is published on GitHub as an MIT-licensed scanner for local, read-only network auditing.
Built for home networks and small IT teams
SunsetScan discovers active devices, fingerprints services and hardware, checks software and product lifecycle status, and produces a plain-English report that explains what was found and what to fix next.
The scanner is local, read-only, and designed for practical network hygiene: routers, switches, cameras, NAS devices, printers, access points, web interfaces, SSH, SMB, SNMP, FTP, TLS, DNS, UPnP, and mDNS.
What it checks
Fast host discovery, flexible target input, MAC vendor lookup, hostname resolution, service detection, and optional passive evidence from mDNS, SSDP, and DHCP.
Checks for insecure protocols, anonymous FTP, SMBv1, missing web headers, exposed admin panels, UPnP exposure, and risky TLS or SSH configurations.
Correlates detected service versions with CVE data, software EOL records, and hardware lifecycle data without calling external APIs during the scan.
Generates self-contained HTML and JSON reports with risk scores, severity groups, evidence, plain-English explanations, and prioritized recommendations.
End-of-life intelligence
SunsetScan uses software EOL data from endoflife.date and a dedicated hardware lifecycle database for network gear, cameras, printers, NAS devices, security appliances, access points, and related modules.
The hardware database is continuously maintained and packaged into the scanner update cycle. The public plan is a monthly scanner and database refresh, so users can update the tool and the lifecycle data together.
Ambiguous vendor EOL or discontinued signals are treated as lifecycle review items unless the source confirms that support or security updates have stopped.
Setup and update commands refresh local caches. Actual scans read local data, which keeps assessments predictable and usable without internet access.
The scanner code is MIT licensed. The hardware EOL database artifacts are distributed under CC BY-NC 4.0.
How it works
Run a quick inventory, an IoT-focused pass, or a full assessment against a subnet or host list.
Combine MAC OUI, banners, HTTP fingerprints, TLS certificates, SSH, UPnP, SNMP, Wappalyzer, mDNS, JA3S, and port heuristics.
Map detected versions and models against local CVE, software lifecycle, and hardware lifecycle caches.
Review severity, risk scores, evidence, and numbered remediation steps in a self-contained HTML file.
Reports people can act on
SunsetScan reports group findings by severity and host, show per-device risk scores, and explain each item in direct language: what was found, why it matters, and what to do next.
Install today
The code is open source and available now. Linux is the best supported platform, and WSL2 is the recommended route for Windows users.
curl -fsSL https://raw.githubusercontent.com/NoCoderRandom/sunsetscan/main/bootstrap.sh | bashsudo ./sunsetscan --setup
sudo ./sunsetscan --full-assessment --target 192.168.1.0/24Open source
SunsetScan is developed in the public GitHub repository. The site links directly to the source, release history, issue tracker, and installation instructions so users can inspect the tool before running it.